By Kiki Schirr, {grow} Contributing Columnist
Your Facebook “About” page says where you were born. LinkedIn states where you work. Your Twitter profile reveals your collegiate team. And that old OKCupid profile you forgot to delete–well, you were a little too open, perhaps.
There’s likely a ton of data about you online, especially if you’re crafting a big social media presence. Being found is great in business, but are you sharing too much private information?
Today I’ll examine the nefarious practice of social engineering and what you can do to combat it.
Keeping yourself safe from social engineering
Social engineering, in the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information. A type of confidence trick for the purpose of information gathering, fraud, or system access, it differs from a traditional “con” in that it is often one of many steps in a more complex fraud scheme.
Let’s start with the basics. What private information is already out there that could be clues for hackers? In order to fully protect your privacy, you should know what you should be guarding. At the least, protect:
- your personal or home phone number
- home address
- your personal email
- state-issued ID numbers
- any information that would hint to a password
If you have a child, or other special considerations, keep even more information secure.
Common types of information-gathering attacks
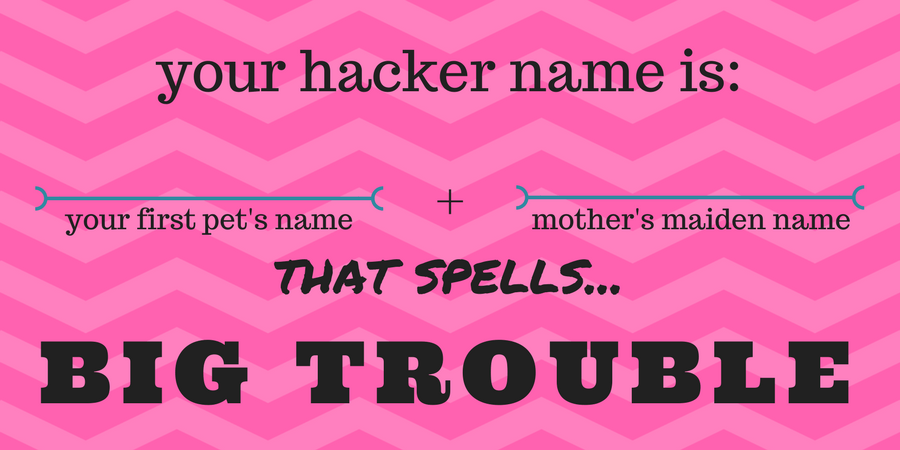
You might have heard that your “hacker name” is the name of your first pet followed by the your mother’s maiden name. Don’t post the results online, because that quiz is a common social engineering attack. Both pieces of information are common answers to identity-proving questions.
There are plenty of other social engineering tactics. You might be familiar with phishing attacks — those are the emails you receive daily in your spam folder, from businesses that look real, asking you to verify private information. A good rule of thumb to combat these attacks is to NEVER click a link in an email, even from your mother. Just type in the root of the URL and search for the content she sent.
Other attacks are more straightforward. They might reward you with some small prize like a song download in exchange for some private information. Both the information you willingly grant them, and the download itself could be malicious.
Also be wary of people offering to fix issues for you. If someone says they can stop the deluge of spam emails your business is getting, it’s quite likely that they are directing the emails in the first place. It’s modern-day protection money.
Tools and tips to protect your private information
Anytime you transfer information via the Internet there’s an opportunity for that conversation to be overheard. Try to only send personal information over websites whose URL begins with “https.”
Also be aware that you don’t necessarily need to hit the send button for a website to read what you’re typing into a form. In 2013, people became aware that Facebook was saving what they’d typed (and deleted!) on the site.
To protect your email, have several accounts and use each one for a purpose. Have a work email, a consulting email, an email for spam, and one for personal contacts. When you don’t trust a site, use your spam email, or create a burner email through tools like Throttle.
If a site or someone that you don’t trusts asks for your phone number, consider using an alternate phone number, such as a Google Voice account, or phone number apps like Ring4.
In the same manner, if someone wants to mail you something, use a post office box.
Never sign in to your bank accounts or give people your information when you’re using a public wifi hotspot. Wait until you get home or on to your company’s secured network.
Best practices for protecting private information
- Don’t save your passwords to your browser in case a device is stolen. Have your device automatically lock after a period of inactivity and set up the remote wipe feature now
- Use complex passwords and do not use one password for multiple locations
- Shop on trusted sites, like Amazon
- Have an extra email address for spam
- Only trust the cloud so much, do not automatically upload sensitive images
- Prevaricate: use an address slightly down the street when getting directions to or from your home and if someone asks where you’re from, don’t name the county where you got your birth certificate
- Porn, pills, and pop stars: searching for adult content, medical supplies, or celebrity gossip can land you on suspicious sites. If you do search in these three categories, use Chrome and be careful where you click
- Remember that while you can forget your password if you need to, you cannot forget your fingerprint. If something is highly sensitive, do not make it accessible through your fingerprint alone
I hope these tips are useful to you. Have fun on the web, but be careful out there!
 Kiki Schirr is a freelance marketer. She is currently building a video platform called WeKiki and draws Tech Doodles. Kiki can be reached easily through Twitter.
Kiki Schirr is a freelance marketer. She is currently building a video platform called WeKiki and draws Tech Doodles. Kiki can be reached easily through Twitter.




 You’re in marketing for one reason: Grow. Grow your company, reputation, customers, impact, profits. Grow yourself. This is a community that will help. It will stretch your mind, connect you to fascinating people, and provide some fun along the way. I am so glad you’re here. -Mark Schaefer
You’re in marketing for one reason: Grow. Grow your company, reputation, customers, impact, profits. Grow yourself. This is a community that will help. It will stretch your mind, connect you to fascinating people, and provide some fun along the way. I am so glad you’re here. -Mark Schaefer